Difference between Kerberos v4 and Kerberos v5
Key difference: Both Kerberos version 4 and version 5 are updates of the Kerberos software. Kerberos v4 is the predecessor of Kerberos v5.
 Kerberos is a web-based software used for providing authentication to user identities and user requests. The internet can be a very insecure place. It often involves the exchange of some sensitive information related to users such as their usernames, passwords, financial details, etc. Such information once exchanged can be subject to a wide range of scrutiny by hackers and malfeasants. At times, a website may experience heavy user traffic. In such a scenario, it becomes easy for the hackers and other offenders to sniff out details from the users and use them to their (hacker's) advantage.
Kerberos is a web-based software used for providing authentication to user identities and user requests. The internet can be a very insecure place. It often involves the exchange of some sensitive information related to users such as their usernames, passwords, financial details, etc. Such information once exchanged can be subject to a wide range of scrutiny by hackers and malfeasants. At times, a website may experience heavy user traffic. In such a scenario, it becomes easy for the hackers and other offenders to sniff out details from the users and use them to their (hacker's) advantage.
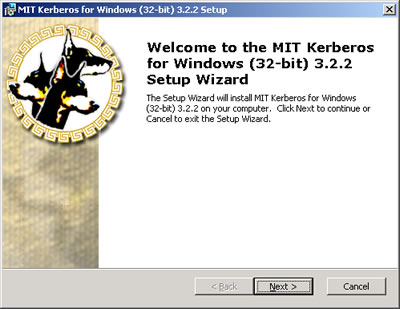
For eliminating such nuisance, the Kerberos software was developed. The word ‘Kerberos’ is derived from Greek mythology, where it stands for the name of the three-headed dog that guarded the gates of Hades. Kerberos was first developed and put in use at the Massachusetts Institute of Technology (MIT). The first three versions of this software operated within the MIT campus itself. It was not until the late 1980’s that Kerberos was made available to the masses and the internet through the release of its version 4 software. Primarily developed for MIT’s very own Project Athena, Kerberos was chiefly designed by Steve Miller and Clifford Neuman.
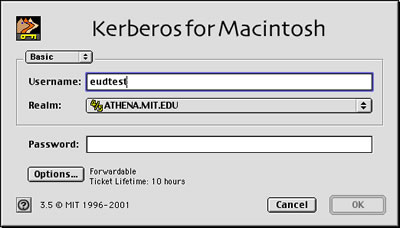 The functioning of Kerberos is based on the authentication server (AS). This type of server is essential for providing users with ‘tickets’, which validate their requests. For instance, if a user requests for a payment service, the authentication server would automatically generate a particular session key and ID, using which the user puts in his/her details and obtains the service. This is where Kerberos comes into the picture. These passwords and other information are in an exposed form on the wire. With the help of Kerberos software, vital data like this is encrypted and protected regularly at every stage of the transaction.
The functioning of Kerberos is based on the authentication server (AS). This type of server is essential for providing users with ‘tickets’, which validate their requests. For instance, if a user requests for a payment service, the authentication server would automatically generate a particular session key and ID, using which the user puts in his/her details and obtains the service. This is where Kerberos comes into the picture. These passwords and other information are in an exposed form on the wire. With the help of Kerberos software, vital data like this is encrypted and protected regularly at every stage of the transaction.
After publishing the version 4 in the fag end of the 1980’s, Clifford Neuman collaborated with John Kohl, to present Kerberos version 5, which was an update of the Kerberos version 4. The version 4 had experienced many limitations and security problems due to the advancement of technology around it. As a result, the version 4 became obsolete and had to be replaced by RFC 1510, or the Kerberos version 5, in the year 1993.
Comparison between Kerberos version 4 and version 5:
|
|
Kerberos Version 4 |
Kerberos Version 5 |
|
Chronology |
Kerberos v4 was released prior to the version 5 in the late 1980’s. |
The version 5 was published in 1993, years after the appearance of version 5. |
|
Key salt algorithm |
Uses the principal name partially. |
Uses the entire principal name. |
|
Encoding |
Uses the “receiver-makes-right” encoding system. |
Uses the ASN.1 coding system. |
|
Ticket support |
Satisfactory |
Well extended. Facilitates forwarding, renewing and postdating tickets. |
|
Network addresses |
Contains only a few IP addresses and other addresses for types of network protocols. |
Contains multiple IP addresses and other addresses for types of network protocols. |
|
Transitive cross-realm authentication support |
No present support for the cause. |
Reasonable support present for such authentication. |
Image Courtesy: oucs.ox.ac.uk, web.mit.edu








Add new comment