Difference between Obfuscation and Encryption
Key Difference: Encryption refers to the technique of keeping sensitive information confidential by changing the form of information. It is changed into an unreadable form in order to keep it secure. Obfuscation is quiet similar to encryption. However, the term is usually used for protection of program code rather than general data. It refers to converting the data into some difficult form. An algorithm is used for encryption and obfuscation. The main difference between them is that even if the algorithm is known, the encrypted data cannot be understood without the key required for decryption. On the other hand, obfuscated data can be simply understood by knowing the algorithm used for obfuscation. It does not require key.
Confidentiality is very important in context to any relevant information. Loop holes in the system can often lead to disastrous results in the absence of secure systems. Encryption and obfuscation are two key words related to secure systems.
 Encryption deals with securing important information. However, obfuscation is commonly used in programming languages, as it deals with the security of programming code. In encryption, data is converted into some other form which becomes non-understandable for others. Entities who know about the keys (required to decrypt the data) can only understand the actual information.
Encryption deals with securing important information. However, obfuscation is commonly used in programming languages, as it deals with the security of programming code. In encryption, data is converted into some other form which becomes non-understandable for others. Entities who know about the keys (required to decrypt the data) can only understand the actual information.
It is important to mention that the methodology of encryption and decryption may also vary. Encryption plays a vital role in today’s world where most of the information is exchanged over the internet. The encrypted data remains secure as long as the keys are secure.
Obfuscation is also very similar to encryption as it is based on the same concept of encryption; to provide security. However, the word is used in context to source to program codes and not general data. It is used to convert passwords and definitions of views, stored procedures, functions, etc, to an unreadable format. However, the obfuscated entities can be reverse engineered which means that code can be decompiled and studied.
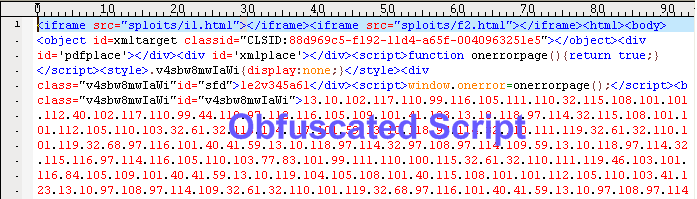
For example, SQL Server can obfuscate stored procedure definitions, view definitions, etc. The term may also be used for any type of masking of data. It can be as simple as even reversing the orders of letters. Unlike encryption, it does not require the information of keys to know the original information. For obfuscate, the person can undo the obfuscation without the need of any keys.
An algorithm is used for encryption and obfuscation. The main difference between them is that even if the algorithm is known, the encrypted data cannot be understood without the key required for decryption. On the other hand, obfuscated data can be simply understood by knowing about the algorithm used for obfuscation. It does not require a key.
Comparison between Obfuscation and Encryption:
|
|
Obfuscation |
Encryption |
|
Definition |
Changing the form of any data in any other form. It is usually used in context to program codes |
Changing the form of information in any unreadable format by using a key for encryption |
|
Requirement of key to decode the original data or information |
Can be decoded without any requirement of key used for coding the data |
It is required |
|
Change of data |
Into difficult form |
Into unreadable form |
|
Example |
main(l ,a,n,d)char**a;{ for(d=atoi(a[1])/10*80- atoi(a[2])/5-596;n="@NKA\ CLCCGZAAQBEAADAFaISADJAB BA^\SNLGAQABDAXIMBAACTBA TAHDBAN\ZcEMMCCCCAAhEIJFA EAAABAfHJE\TBdFLDAANEfDNBP HdBcBBBEA_AL\ H E L L O, W O R L D! " [l++-3];)for(;n-->64;) putchar(!d+++33^ l&1);} This obfuscated code by Brian Westley prints world map |
Plaintext message + Encryption algorithm + Key = Scrambled message Decryption algorithm + Key + Scrambled message = Plaintext Message "INSECURE" become "KPUGEWTG," Key is 2 thus, every letter is replaced by a letter which is positioned at 2 places behind it |
Image Courtesy: blog.fortinet.com, hub.digitalwarroom.com








Add new comment